Hello,
Je viens solliciter votre aide car je ne trouve pas de solution au piratage de mon routeur Asus RT-AC66U.
Ce qui me faire dire que je me suis fait pirater ce routeur, c'est des requêtes quotidiennes de login sur mon NAS synology qui viennent de mon routeur...
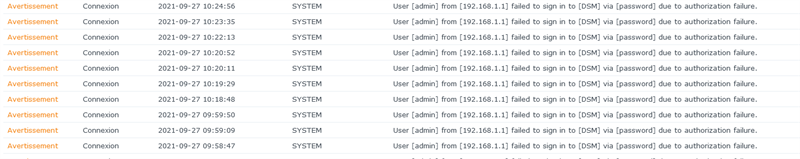
Je m'en suis rendu compte il y a un mois. Je pensais qu'il y avait une faille dans le VPN OpenVPN que j'avais activé, j'ai donc désactivé, mais pareil.
Je tente un factory reset, pareil. Je force une MAJ de firmware, je découvre que Asus en a sorti un qui n'est pas accessible par la mise à jour interne , joie, je mets à jour le firmware et toujours pareil, toujours ces requêtes qui viennent du 192.168.1.1 !
Aucune trace dans les logs du routeur , mais je poste le log de démarrage, y'a pas mal de truc que je trouve bizarres et que je ne comprends pas..
Quelqu'un peut m'aider ?
Sep 27 11:37:36 rc_service: httpd 571:notify_rc reboot
Sep 27 11:37:36 FTP Server: daemon is stoped
Sep 27 11:37:36 Samba Server: smb daemon is stoped
Sep 27 11:37:37 WEBDAV Server: daemon is stoped
May 5 07:05:02 syslogd started: BusyBox v1.17.4
May 5 07:05:02 kernel: klogd started: BusyBox v1.17.4 (2021-01-28 20:44:39 CST)
May 5 07:05:02 kernel: start_kernel
May 5 07:05:02 kernel: Linux version 2.6.22.19 (root@asus) (gcc version 4.2.3) #1 Thu Jan 28 20:46:30 CST 2021
May 5 07:05:02 kernel: CPU revision is: 00019749
May 5 07:05:02 kernel: Found an ST compatible serial flash with 32 64KB blocks; total size 2MB
May 5 07:05:02 kernel: Determined physical RAM map:
May 5 07:05:02 kernel: memory: 07fff000 @ 00000000 (usable)
May 5 07:05:02 kernel: memory: 08000000 @ 87fff000 (usable)
May 5 07:05:03 kernel: Built 1 zonelists. Total pages: 585216
May 5 07:05:03 kernel: Kernel command line: root=/dev/mtdblock3 console=ttyS0,115200 init=/sbin/preinit
May 5 07:05:03 kernel: Primary instruction cache 32kB, physically tagged, 4-way, linesize 32 bytes.
May 5 07:05:03 kernel: Primary data cache 32kB, 4-way, linesize 32 bytes.
May 5 07:05:03 kernel: PID hash table entries: 2048 (order: 11, 8192 bytes)
May 5 07:05:03 kernel: CPU: BCM5300 rev 1 pkg 0 at 600 MHz
May 5 07:05:03 kernel: Using 300.000 MHz high precision timer.
May 5 07:05:03 kernel: Dentry cache hash table entries: 65536 (order: 6, 262144 bytes)
May 5 07:05:03 kernel: Inode-cache hash table entries: 32768 (order: 5, 131072 bytes)
May 5 07:05:03 kernel: _ Reboot message ... _______________________________________________________
May 5 07:05:03 kernel: >>> Restarting system.
May 5 07:05:03 kernel: >>> Please stand by while rebooting the system...
May 5 07:05:03 kernel: >>>
May 5 07:05:03 kernel: ____________________________________________________________________________
May 5 07:05:03 kernel: Mount-cache hash table entries: 512
May 5 07:05:03 kernel: PCI: Initializing host
May 5 07:05:03 kernel: PCI: Reset RC
May 5 07:05:03 kernel: PCI: Initializing host
May 5 07:05:03 kernel: PCI: Reset RC
May 5 07:05:03 kernel: PCI: Fixing up bus 0
May 5 07:05:03 kernel: PCI/PCIe coreunit 0 is set to bus 1.
May 5 07:05:03 kernel: PCI: Fixing up bridge
May 5 07:05:03 kernel: PCI: Fixing up bridge
May 5 07:05:03 kernel: PCI: Enabling device 0000:01:00.1 (0004 -> 0006)
May 5 07:05:03 kernel: PCI: Fixing up bus 1
May 5 07:05:03 kernel: PCI/PCIe coreunit 1 is set to bus 2.
May 5 07:05:03 kernel: PCI: Fixing up bridge
May 5 07:05:03 kernel: PCI: Fixing up bridge
May 5 07:05:03 kernel: PCI: Enabling device 0000:02:00.1 (0004 -> 0006)
May 5 07:05:03 kernel: PCI: Fixing up bus 2
May 5 07:05:03 kernel: IP route cache hash table entries: 4096 (order: 2, 16384 bytes)
May 5 07:05:03 kernel: TCP established hash table entries: 16384 (order: 5, 131072 bytes)
May 5 07:05:03 kernel: TCP bind hash table entries: 16384 (order: 4, 65536 bytes)
May 5 07:05:03 kernel: highmem bounce pool size: 64 pages
May 5 07:05:03 kernel: pflash: found no supported devices
May 5 07:05:03 kernel: Boot partition size = 262144(0x40000)
May 5 07:05:03 kernel: Creating 2 MTD partitions on "sflash":
May 5 07:05:03 kernel: 0x00000000-0x00040000 : "pmon"
May 5 07:05:03 kernel: 0x001f0000-0x00200000 : "nvram"
May 5 07:05:03 kernel: Found a Zentel NAND flash with 2048B pages or 128KB blocks; total size 128MB
May 5 07:05:03 kernel: lookup_nflash_rootfs_offset: offset = 0x0
May 5 07:05:03 kernel: nflash: squashfs filesystem found at block 9
May 5 07:05:03 kernel: Creating 4 MTD partitions on "nflash":
May 5 07:05:03 kernel: 0x00000000-0x02000000 : "linux"
May 5 07:05:03 kernel: 0x001357a0-0x02000000 : "rootfs"
May 5 07:05:03 kernel: 0x04000000-0x06000000 : "linux2"
May 5 07:05:03 kernel: 0x041357a0-0x06000000 : "rootfs2"
May 5 07:05:03 kernel: Creating 3 MTD partitions on "brcmnand":
May 5 07:05:03 kernel: 0x00000000-0x02000000 : "trx"
May 5 07:05:03 kernel: 0x04000000-0x06000000 : "asustrx2"
May 5 07:05:03 kernel: 0x06000000-0x07f00000 : "brcmnand"
May 5 07:05:03 kernel: dev_nvram_init: _nvram_init
May 5 07:05:03 kernel: u32 classifier
May 5 07:05:04 kernel: Netfilter messages via NETLINK v0.30.
May 5 07:05:04 kernel: nf_conntrack version 0.5.0 (2048 buckets, 16384 max)
May 5 07:05:04 kernel: ip_tables: (C) 2000-2006 Netfilter Core Team
May 5 07:05:04 kernel: net/ipv4/netfilter/tomato_ct.c [Jan 28 2021 20:46:08]
May 5 07:05:04 kernel: ip6_tables: (C) 2000-2006 Netfilter Core Team
May 5 07:05:04 kernel: VFS: Mounted root (squashfs filesystem) readonly.
May 5 07:05:04 kernel: Warning: unable to open an initial console.
May 5 07:05:04 kernel: Failed to execute /sbin/preinit. Attempting defaults...
May 5 07:05:04 kernel: ctf: module license 'Proprietary' taints kernel.
May 5 07:05:04 kernel: et_module_init: passivemode set to 0x0
May 5 07:05:04 kernel: et_module_init: et_txq_thresh set to 0xce4
May 5 07:05:04 kernel: bcm_robo_enable_switch: EEE is disabled
May 5 07:05:04 kernel: eth0: Broadcom BCM47XX 10/100/1000 Mbps Ethernet Controller 6.30.163.2002 (r382208)
May 5 07:05:04 kernel: wl_module_init: passivemode set to 0x0
May 5 07:05:04 kernel: PCI: Enabling device 0000:01:01.0 (0000 -> 0002)
May 5 07:05:04 kernel: eth1: Broadcom BCM4331 802.11 Wireless Controller 6.30.163.2002 (r382208)
May 5 07:05:04 kernel: PCI: Enabling device 0000:02:01.0 (0000 -> 0002)
May 5 07:05:04 kernel: eth2: Broadcom BCM4360 802.11 Wireless Controller 6.30.163.2002 (r382208)
May 5 07:05:04 kernel: Algorithmics/MIPS FPU Emulator v1.5
May 5 07:05:04 kernel: wlc_phy_cal_init_acphy: NOT Implemented
May 5 07:05:04 nat: apply redirect rules
May 5 07:05:09 acsd: selected channel spec: 0x1904 (6u)
May 5 07:05:09 acsd: acs_set_chspec: 0x1904 (6u) for reason APCS_INIT
May 5 07:05:09 WAN Connection: ISP's DHCP did not function properly.
May 5 07:05:10 acsd: selected channel spec: 0xe02a (36/80)
May 5 07:05:10 acsd: acs_set_chspec: 0xe02a (36/80) for reason APCS_INIT
May 5 07:05:10 RT-AC66U: start httpd:80
May 5 07:05:10 httpd: Save SSL certificate...80
May 5 07:05:11 httpd: Succeed to init SSL certificate...80
May 5 07:05:12 jffs2: valid logs(1)
May 5 07:05:12 disk monitor: be idle
May 5 07:05:12 hour monitor: daemon is starting
May 5 07:05:12 hour monitor: daemon terminates
May 5 07:05:13 Mastiff: init
May 5 07:05:14 syslog: module ax88179_178a not found in modules.dep
May 5 07:05:15 syslog: module ledtrig-usbdev not found in modules.dep
May 5 07:05:15 syslog: module leds-usb not found in modules.dep
May 5 07:05:15 kernel: SCSI subsystem initialized
May 5 07:05:19 rc_service: udhcpc 731:notify_rc start_firewall
May 5 07:05:19 nat: apply nat rules (/tmp/nat_rules_eth0_eth0)
May 5 07:05:19 wan: finish adding multi routes
May 5 07:05:19 rc_service: udhcpc 731:notify_rc stop_upnp
May 5 07:05:19 rc_service: waitting "start_firewall" via udhcpc ...
May 5 07:05:20 WAN Connection: WAN was restored.
May 5 07:05:20 rc_service: udhcpc 731:notify_rc start_upnp
May 5 07:05:20 rc_service: waitting "stop_upnp" via udhcpc ...
May 5 07:05:22 ntp: start NTP update
Sep 27 11:38:43 rc_service: ntp 767:notify_rc restart_diskmon
Sep 27 11:38:43 disk_monitor: Finish
Sep 27 11:38:43 disk monitor: be idle
Sep 27 11:38:44 dhcp client: bound 93.25.177.XX/255.255.254.0 via 93.25.176.1 for 14400 seconds.
Sep 27 11:39:21 crond[580]: time disparity of 1787314 minutes detected
Sep 27 11:40:31 WATCHDOG: [FAUPGRADE][auto_firmware_check 5735)]periodic_check AM 5:21
5735)]periodic_check AM 5:21
Message édité par garfield67540 le 27-09-2021 à 14:23:58
---------------
Hexa MK









